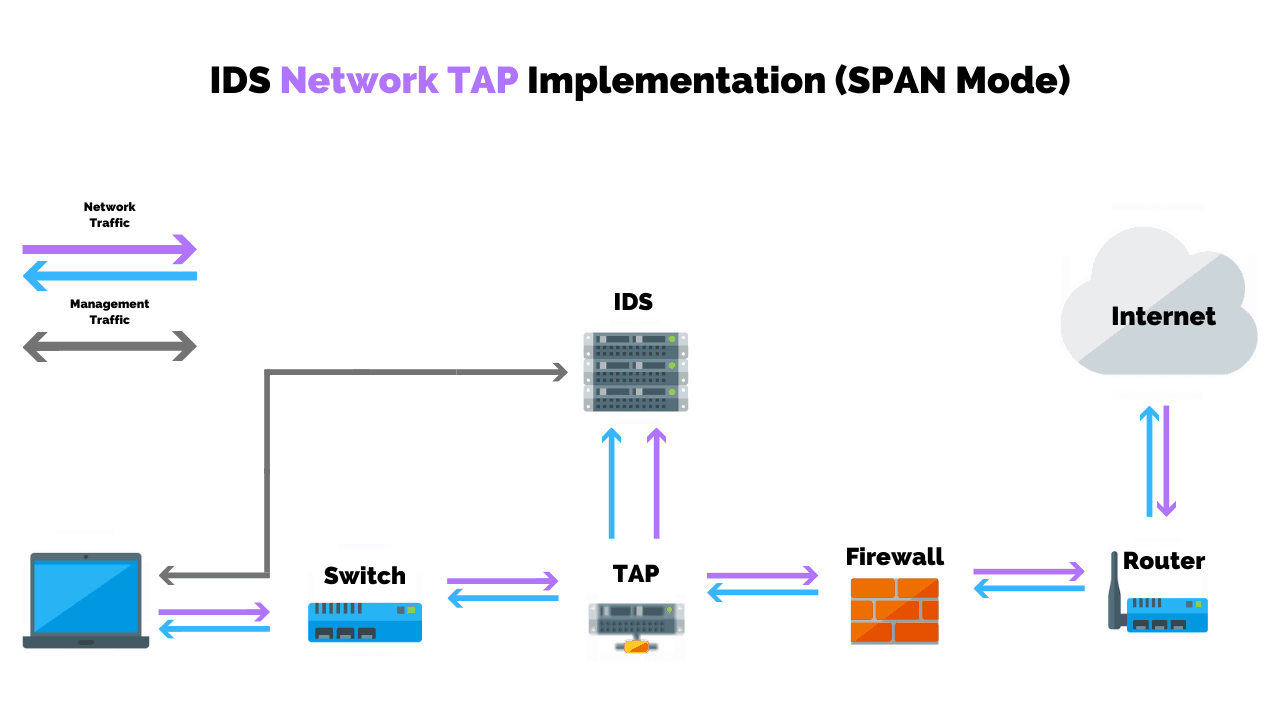
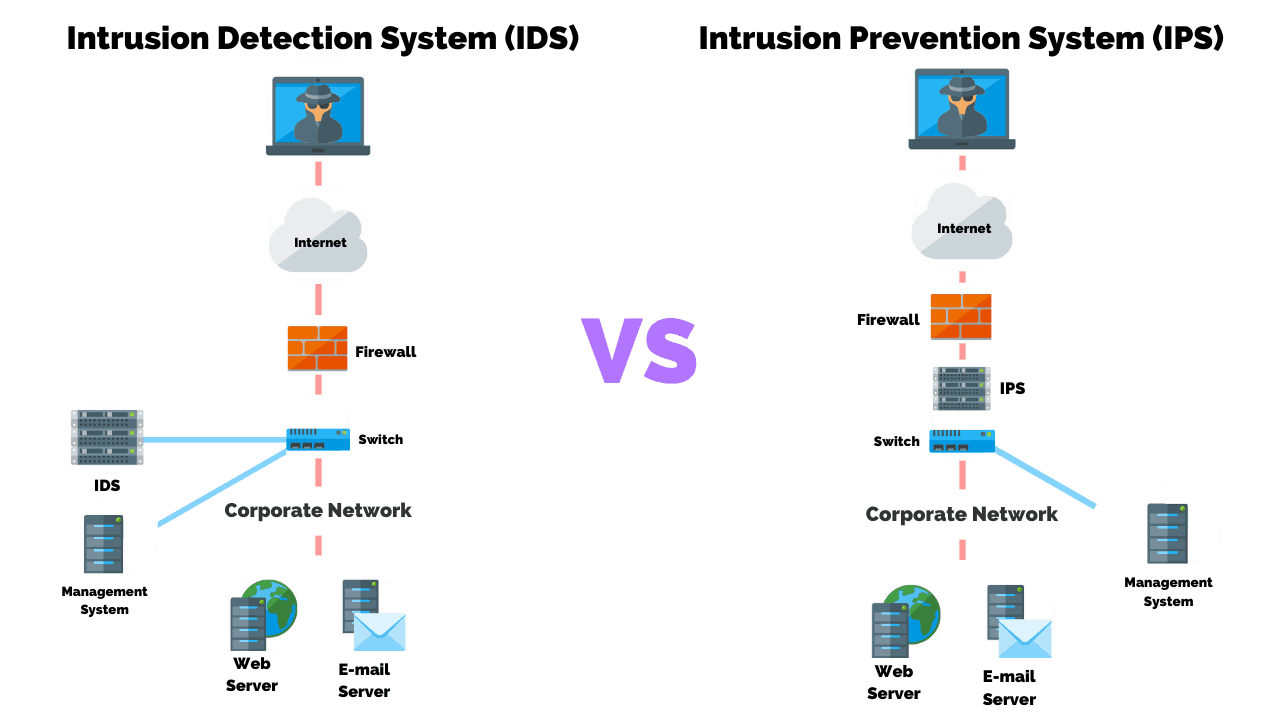
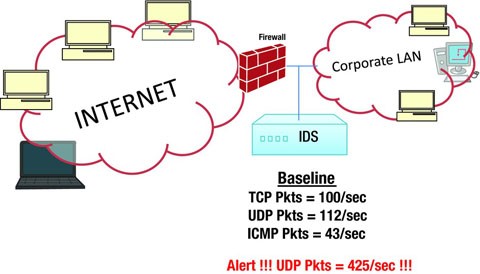
What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices | Spiceworks It Security

What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices | Spiceworks It Security
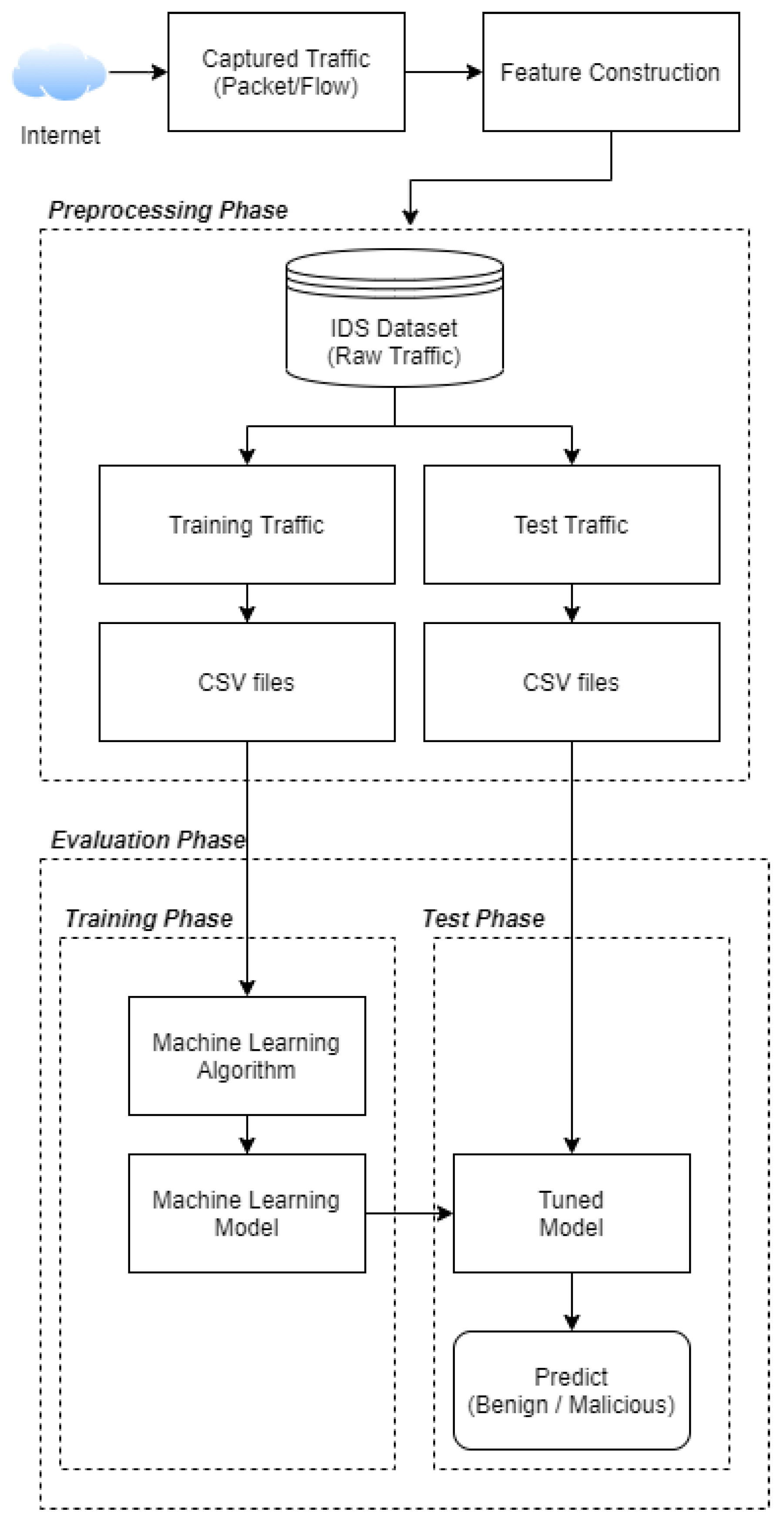
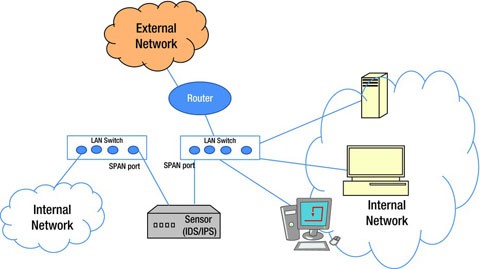
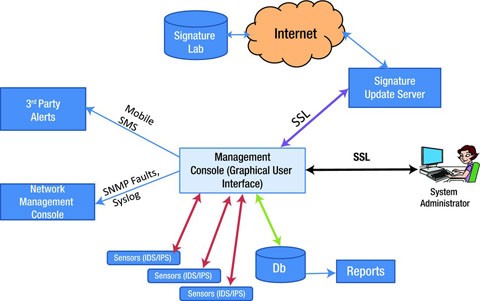
Applied Sciences | Free Full-Text | Generating Network Intrusion Detection Dataset Based on Real and Encrypted Synthetic Attack Traffic | HTML
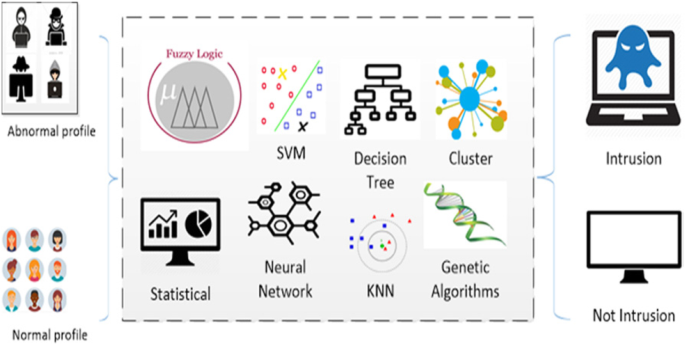
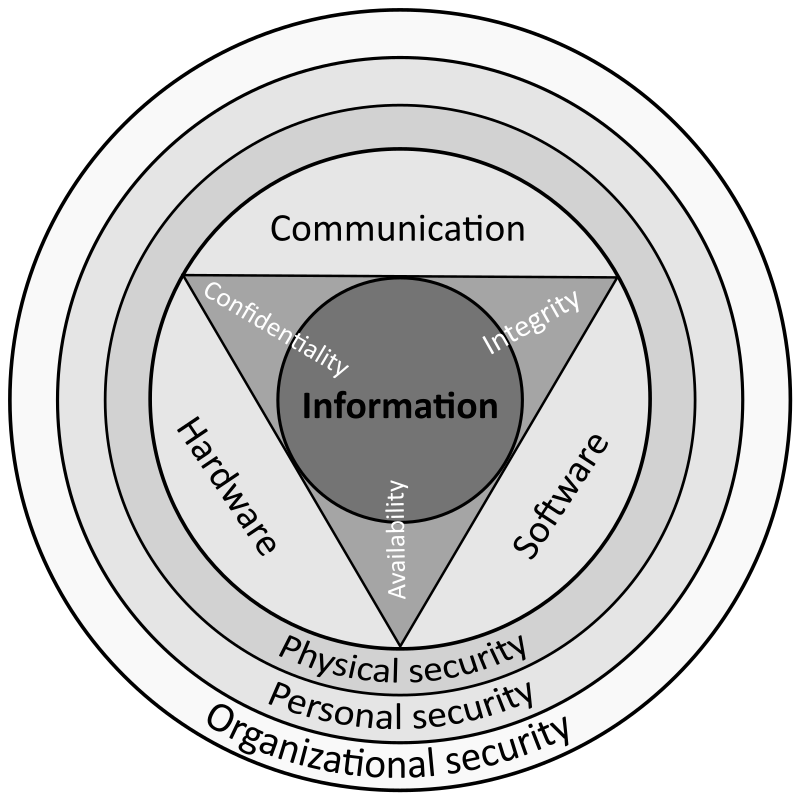
Survey of intrusion detection systems: techniques, datasets and challenges | Cybersecurity | Full Text